
PDF) Implementation of White-Box Cryptography in Credit Card Processing Combined with Code Obfuscation

Implementation of White-Box Cryptography in Credit Card Processing Combined with Code Obfuscation | Semantic Scholar

PDF) Implementation of White-Box Cryptography in Credit Card Processing Combined with Code Obfuscation | sarvesh tanwar - Academia.edu










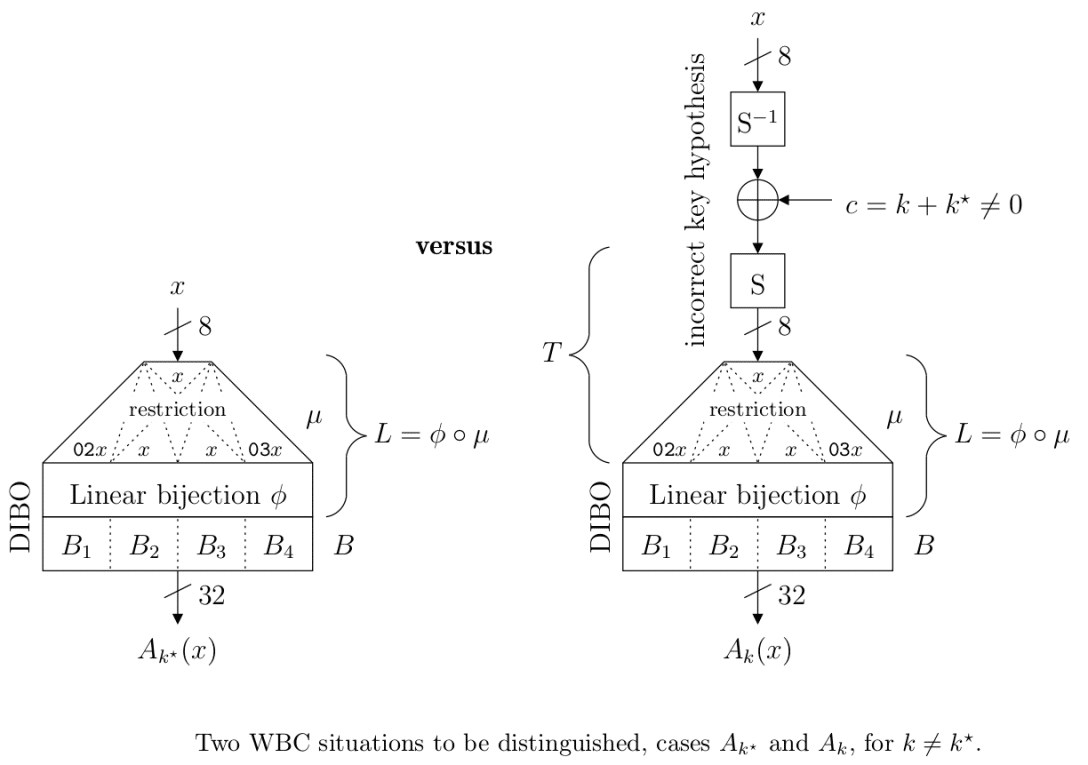
![PDF] White-Box Cryptography and an AES Implementation | Semantic Scholar PDF] White-Box Cryptography and an AES Implementation | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/8714edde0892559602ad4239e80ec226a1bbe8d8/8-Figure1-1.png)
